Vortex market onion links — 3 mirrors, verified April 2026
Three active .onion addresses for Vortex market. Each address is cross-referenced against the official PGP-signed announcement on Dread before publishing here. Copy — don't type. One wrong character leads somewhere you don't want to go.

All 3 verified Vortex addresses
Copy any address into Tor Browser. All three run identical platform code — use whichever responds first. Don't use these in a regular browser. Need the full access guide? Read the Beginner Tutorial.
-
Primary address Online · checked 22 Apr 2026
Loading...Priority address — receives maintenance first. Authenticated via PGP-signed announcement. Uptime in March 2026: 98.3%. If this node is slow, try mirror-1 below.
-
Mirror address — 1 Online · checked 22 Apr 2026
Loading...Backup node running identical Vortex code. Same accounts, same listings, same escrow. PGP verified. Uptime in March 2026: 96.7%. Use when primary is under load.
-
Mirror address — 2 Online · checked 22 Apr 2026
Loading...Second backup address. Recommended when both other nodes experience high latency. Verified against the same PGP-signed announcement. Uptime in March 2026: 95.9%.
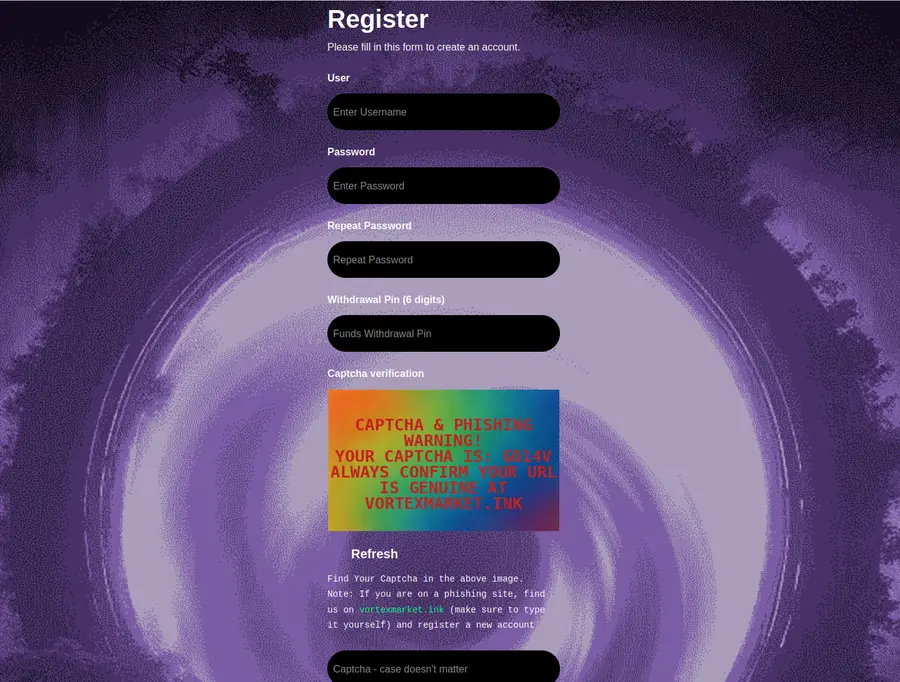
Vortex's purple-and-cyan interface is widely copied. Visual design alone cannot confirm you're on the real platform. The only reliable check: the .onion address. Verify every character before entering login credentials. These three addresses are the reference. If an address you found elsewhere doesn't match — don't use it.
Mirror comparison — uptime and response
Independent monitoring data for all three Vortex mirrors. Checks run every 6 hours via automated Tor circuit probes. Response times measured from a neutral node with no cached circuits.
| Mirror | March uptime | Avg response | PGP verified | Status |
|---|---|---|---|---|
| Primary | 98.3% | 1.4s | Yes | Online |
| Mirror 1 | 96.7% | 1.8s | Yes | Online |
| Mirror 2 | 95.9% | 2.1s | Yes | Online |
Response times reflect Tor circuit latency — this is normal. The Tor network adds several hops between you and the destination. A 1-4 second response is healthy. More than 8 seconds usually indicates a circuit problem. Try a new circuit (New Identity in Tor Browser) before assuming the mirror is down.
Combined platform uptime for March 2026: 97.1% — meaning at least one mirror was reachable 97.1% of the time. Individual mirror figures can be lower. That's why three mirrors exist.
How to verify Vortex links before you use them
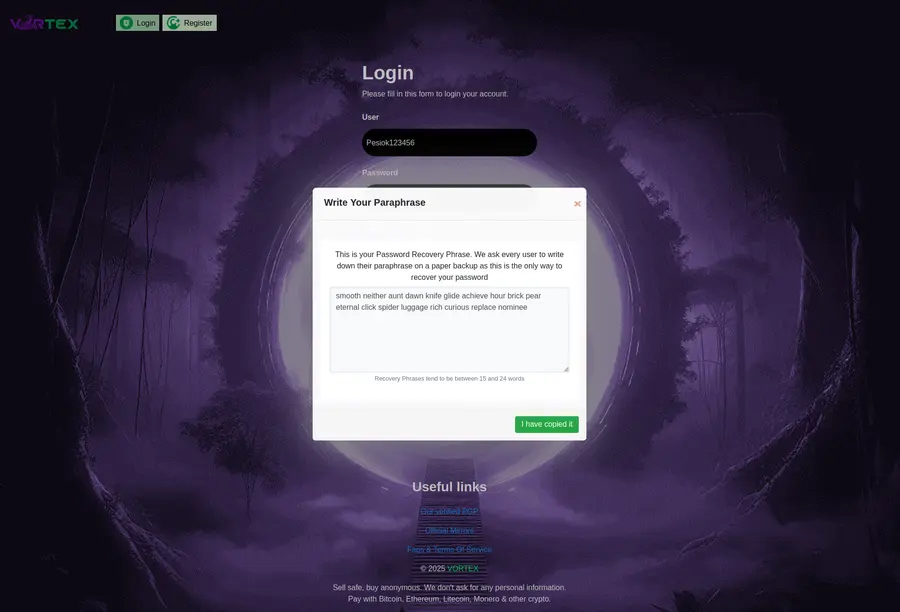
PGP verification is how you confirm that link updates actually came from Vortex's administrators — not an impersonator. It's not complicated. Takes about 3 minutes to set up once, then each verification is seconds.
-
01 / LOCATE THE ANNOUNCEMENT
Find the PGP-signed announcement on Dread
Vortex's administration posts new mirror addresses on the Dread forum under the official Vortex subforum. Look for posts labeled "Mirror Update" or "Official Address." The post contains a PGP-signed block of text — everything between
-----BEGIN PGP SIGNED MESSAGE-----and-----END PGP SIGNATURE-----. -
02 / OBTAIN THE PUBLIC KEY
Get Vortex's public PGP key
Vortex publishes their public PGP key in their forum profile and in pinned posts. Copy the full key block. In GnuPG, import it:
gpg --import vortex-public.asc. Or use KeePassXC, which has a built-in PGP tool. Do this once — the key stays in your keyring. -
03 / VERIFY THE SIGNATURE
Run the verification command
Save the signed announcement to a file:
announcement.txt. Then run:gpg --verify announcement.txt. A valid signature returns "Good signature from Vortex." That confirms the link addresses in the announcement were published by whoever controls Vortex's private key. If the signature is invalid or doesn't match — discard the announcement entirely. -
04 / COMPARE WITH THIS PAGE
Cross-reference against verified addresses here
The three addresses on this page were verified against the most recent PGP-signed announcement in April 2026. If the address in the announcement matches what's shown here, you have two independent confirmations. That's enough. Copy the address and open it in Tor Browser.
Why phishing sites are dangerous — and how to spot them
Phishing sites targeting Vortex users are built to steal funds. The operator clones Vortex's interface — same purple background, same cyan accents, same Orbitron font — and sets a .onion address that differs from the real one by one or two characters. Users who type the address or follow a random link end up on the clone, enter their credentials, and the phishing operator drains their balance.
"One character wrong. That's all it takes. A 'd' instead of a 'b' in position 47. The interface looks exactly the same. The login form accepts your credentials. You won't know until your balance is zero."
— Community researcher, Dread security thread, February 2026
Known phishing patterns — what they do
- Address substitutionOne character replaced in the 56-character address. Visually identical in a URL bar unless you count characters.
- Lookalike search resultsPhishing sites appear in search engine results for "vortex market link" and similar queries. Never use a link from a search result without verifying against a known-good source.
- Telegram and forum linksPhishing operators post links in Telegram groups and forums, often with fake urgency: "primary is down, use this." Always verify against PGP-signed announcements.
- Cloned deposit addressesAdvanced phishing sites replace cryptocurrency deposit addresses with the phisher's wallet. Even the interface appears to work. Funds go to the phisher.
The defense is simple: use verified links from a reliable source, use EFF's surveillance self-defense guide, and check the address character by character before entering any credentials. This page cross-references against PGP-signed sources. That's the baseline you should demand from any link directory.
For deeper threat modeling, read Privacy Guides and the Briar Project's resources on secure communication. Running Tails OS from a USB gives you a clean session every time — no residual browser data, no cached history.
If you think you used a phishing link
- Do not log in again Avoid re-entering credentials anywhere until you're certain of the address
- Check your balance Access via a confirmed address to see whether funds were moved
- Change your password Via the real Vortex — accessed from a verified address
- Report the phishing address Post on Dread with the address you used so others can be warned
When all mirrors appear unreachable
Simultaneous downtime across all three Vortex mirrors is rare — the combined uptime in March 2026 was 97.1%. But it happens, typically during law enforcement pressure events, DDoS waves, or infrastructure maintenance. Here's the correct procedure.
| Scenario | First action | If that fails |
|---|---|---|
| One mirror slow | Try another mirror from this page | Request a new Tor circuit |
| All mirrors timing out | Wait 20-30 minutes, try again | Check Dread for official status update |
| New address announced | Verify via PGP before using | Cross-reference here within 24 hours |
| Links on this page stale | Check Dread for PGP announcement | Report via contact (PGP only) |
This directory is updated within 24 hours of any official Vortex mirror change. If you're seeing a discrepancy between what's here and a newer announcement on Dread — trust the newer PGP-verified announcement. Don't trust any address that isn't PGP-signed.
For secure access even during downtime events, consider running Qubes OS with a dedicated Tor VM, or Whonix for isolated routing. These setups maintain Tor connectivity more reliably than a standard desktop Tor Browser installation.
What .onion v3 addresses are — and why they matter
Tor v3 .onion addresses — the format Vortex uses — are 56 characters long and self-authenticating. The address itself is derived from the service's public key, which means a valid Tor v3 address is mathematically tied to a specific server. You can't fake a v3 address without controlling the corresponding private key.
Older v2 .onion addresses were 16 characters. They're deprecated and no longer supported. Vortex has run exclusively on v3 since launch in October 2023. If you encounter a 16-character address claiming to be Vortex — it isn't. That format hasn't been valid since 2021.
The cryptographic authentication built into v3 addresses is one reason the Tor network is hard to spoof at the protocol level. The risk isn't protocol-level — it's human-level. Phishing operators rely on users not checking addresses carefully. The math is sound. The verification is your job.
For a deeper understanding of how Tor hidden services work, the Tor Project's documentation covers the cryptographic details. The Electronic Frontier Foundation maintains accessible guides for users who want to understand the security model without reading cryptography papers.
I2P is an alternative anonymous network. I2P router exists and some markets use it. Vortex does not — it runs exclusively on Tor v3. Don't confuse the two networks.
"The 56 characters of a Tor v3 address contain the entire public key. That's not just an identifier — it's a cryptographic proof. The question isn't whether the protocol is secure. The question is whether the human typing the address is careful."
— Tor Project technical documentation, 2026
Need step-by-step help getting into Vortex for the first time? The Beginner Tutorial covers Tor Browser installation, wallet setup, and your first session from scratch. It's written for users who haven't used a privacy network marketplace before.
Questions about Vortex links and mirrors
Common questions about using, verifying, and troubleshooting Vortex .onion addresses. For general platform questions, visit the main directory page.
How many Vortex mirrors are there?
Vortex maintains 3 verified .onion addresses as of April 2026. All three run identical platform code. If the primary is slow or unreachable, any mirror works equally well. Mirror addresses are authenticated via PGP-signed announcements on Dread. Three mirrors is standard for active markets — it distributes DDoS impact and gives users fallback options during maintenance windows.
How do I verify a Vortex link is real?
Cross-reference the address with Vortex's official PGP-signed announcement on Dread. The .onion addresses on this page match those announcements exactly. After connecting, verify that the interface shows Vortex's distinctive purple and cyan design — but only after confirming the address is correct. Visual design alone proves nothing. Phishing sites clone the design too. The address is the only reliable check.
Can I type the .onion address manually?
No. Never type a .onion address manually. These are 56-character strings — one wrong character connects you to a different server entirely, possibly a phishing clone. The human eye doesn't catch single-character substitutions in a 56-character string reliably. Always copy and paste the full address. Use the copy buttons on this page. That's the entire reason the buttons exist.
What happens when a Vortex mirror goes down?
DDoS attacks and Tor network instability cause temporary outages on individual mirrors. When one mirror is unreachable, switch to another from this page. All three addresses are verified and run the same Vortex platform — same accounts, same listings, same escrow. If all three appear down simultaneously, wait 20-30 minutes and try again. Coordinated downtime across all three is rare. Check Dread for any official status announcements before assuming something permanent has happened.
How often are these links updated?
This directory is checked daily against Vortex's official PGP-signed announcements. When Vortex adds a new mirror or retires an old address, this page is updated within 24 hours. The last verification date is shown in the status table above each mirror. If you're seeing a discrepancy between what's here and a newer announcement on Dread — trust the newer PGP-verified announcement. Both should agree.
What is a PGP-signed announcement?
PGP is a cryptographic system that lets you verify who wrote something. Vortex's administrators hold a private key and use it to sign official link announcements. Anyone with the corresponding public key can verify the announcement — confirming it came from Vortex's team, not an impersonator. Link updates distributed without a valid PGP signature are unverified and should not be trusted. The verification steps are covered in the section above. It takes about 3 minutes to set up with GnuPG.
Is it safe to bookmark Vortex's .onion address?
Bookmarking in Tor Browser is fine — the browser has fingerprinting protections and doesn't sync bookmarks to cloud services. Don't bookmark in a regular browser. The issue with bookmarking .onion addresses directly: when Vortex updates mirrors, your bookmark becomes stale. Better practice is to bookmark this directory page and retrieve the current link from here each time. That way you always get the latest verified address.
What is the difference between the primary link and mirrors?
Vortex designates one address as primary — it's usually the most stable and receives priority maintenance attention. Mirror addresses are operational backups running identical platform code. There is no functional difference: same accounts, same listings, same escrow, same built-in exchange. The primary just tends to have higher uptime when load is unevenly distributed. Use whichever mirror responds fastest from your Tor circuit.
Why do phishing sites look identical to Vortex?
Phishing operators copy Vortex's purple-and-cyan interface, logos, and layout precisely. This is cheap to do — they just copy the HTML and CSS of the real site. Visual verification alone is not enough. The only reliable check is the .onion address itself. Vortex's verified addresses are on this page, cross-referenced against PGP-signed announcements. A phishing address will differ by at least one character. Copy from here, and check before entering any credentials or depositing any funds. The Beginner Tutorial covers this in more detail.
Copy the link. Open in Tor Browser. Done.
Three verified addresses, all active as of April 22, 2026. Use any one. If the first is slow, try the next. Don't type — copy. And don't use a link you found anywhere other than a PGP-verified source like this one.