Search Bing for "Vortex market onion link" and you get hundreds of results. Most are wrong. Some push fake addresses that look identical to the real login page until you notice the missing character in position 38 of the .onion string. By then, you've typed your credentials into a phishing clone.
This portal exists because that problem is real. Vortex's Tor v3 addresses are 56 characters long. One wrong character is invisible at a glance. The only reliable source is a PGP-signed announcement from the Vortex team — cross-referenced on Dread, the privacy network's primary discussion platform.
We run that cross-reference before publishing each address. And we repeat it every time the sitemap regenerates. The addresses you find on our Active Links page match the most recent PGP-signed announcement exactly. If Vortex rotates a mirror, we update within 24 hours.
The portal is maintained by volunteers who run Tor nodes and monitor Dread for official Vortex announcements. We have no financial relationship with Vortex market. We accept no payments. We index their links so you don't have to trust a random clearnet page you found via DuckDuckGo at 2am.
That said: read EFF's digital security resources and Privacy Guides before you act on anything you find here. Laws differ across jurisdictions. This site is educational.
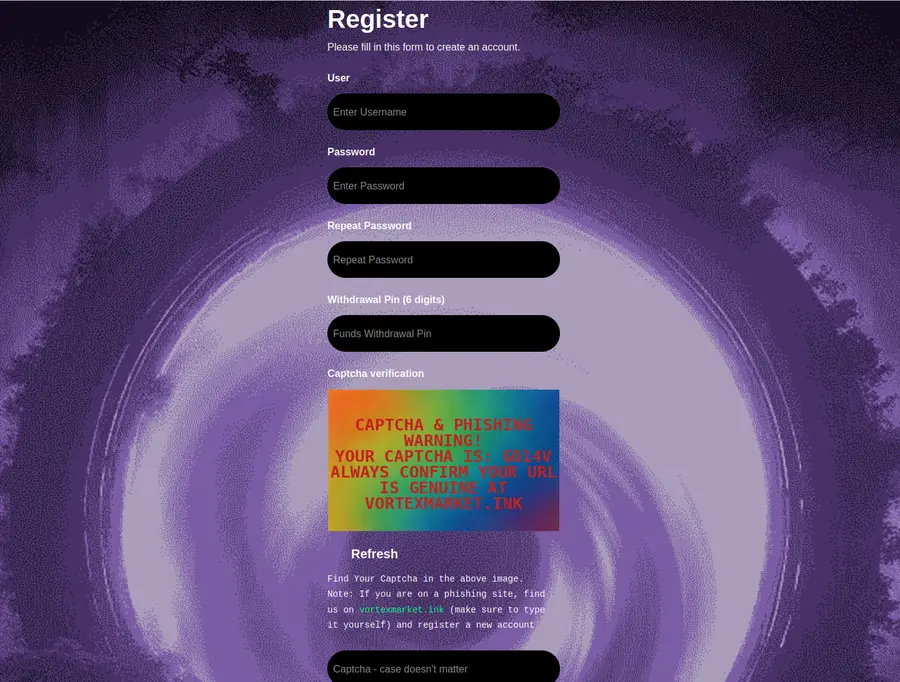
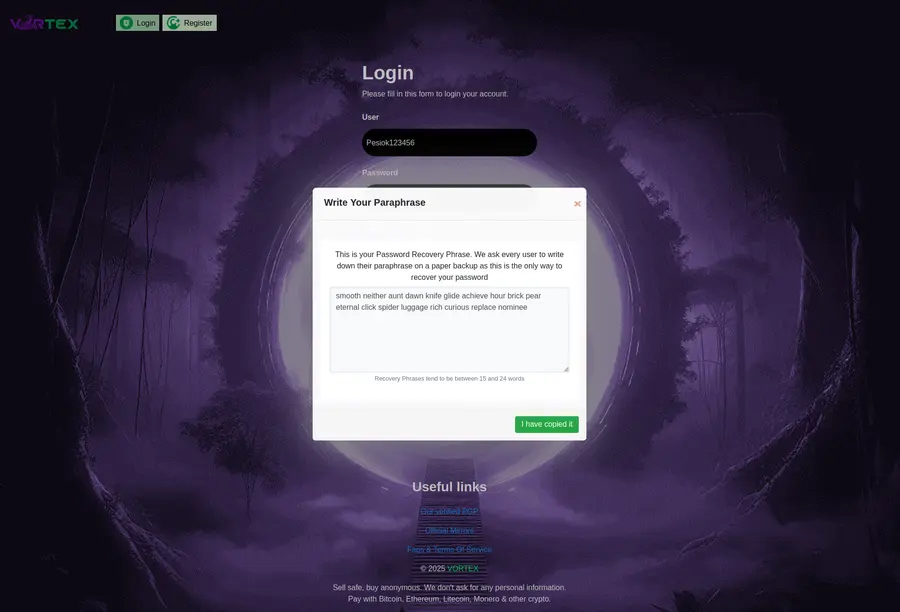
Phishing sites copied Vortex's purple-and-cyan design exactly. The interface looks right. The URL is wrong. Check every character of the .onion address before entering any credentials.
For new users: start with our Beginner Tutorial. It covers Tor Browser installation, PGP key generation, and what to expect on your first login — written plainly, no assumed knowledge.