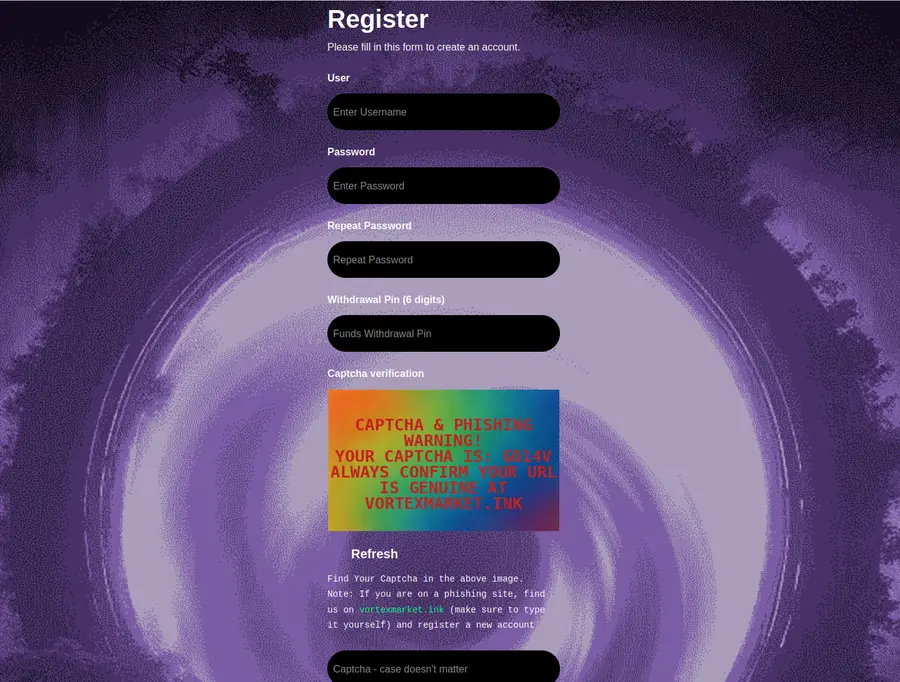
Vortex market opened its doors in October 2023 and grew into a top-ten privacy network marketplace within fifteen months. The timing was deliberate. Hydra had ceased operations in early 2022. Operators of AlphaBay and Wall Street Market were working through long court cases. International law enforcement collaboration had tightened. The ecosystem was nervous. Vortex arrived with a specific pitch: a cleaner interface, a built-in crypto exchange, support for USDT on the TRON network, and a 14-day multisig escrow that matched what experienced buyers already expected from proven platforms.
By March 2026 the platform reported 62,299 registered users, 2,639 approved vendors, and 17,297 active listings. Uptime landed at 97.1% across a rolling 90-day window. The numbers are modest compared to the largest competitors — but the growth direction has been steady, and the onboarding experience has fewer rough edges than platforms that launched before the built-in exchange became a standard expectation.
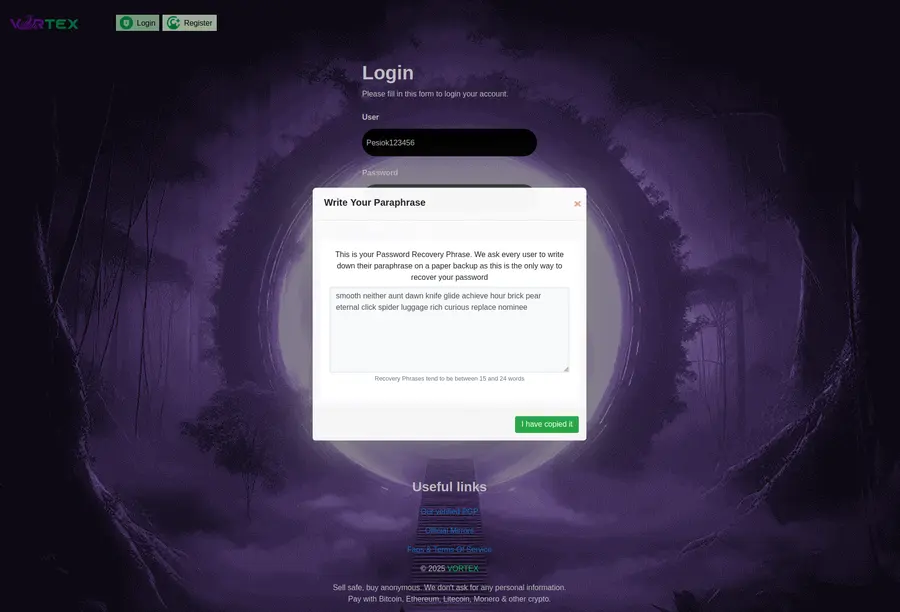
This page is not run by the Vortex team. It is a volunteer-maintained directory. We verify .onion addresses against PGP-signed announcements on Dread, we regenerate the sitemap daily, and we flag any mirror that fails validation. Phishing clones copy the purple-and-cyan brand almost perfectly; they count on users typing the address by hand. That is the specific problem this directory solves. Copy from here, paste into Tor, verify the interface matches, and move on with your day.
We do not rate vendors. We do not broker disputes. We do not claim to have insider knowledge about the platform operators. What we do, narrowly and consistently, is keep three working onion addresses reachable with fresh verification timestamps so the first thirty seconds of your Vortex session are not spent guessing which character in a 56-character address might be wrong. Done right, that is the entire value of an independent directory: remove a specific, common, avoidable failure mode.